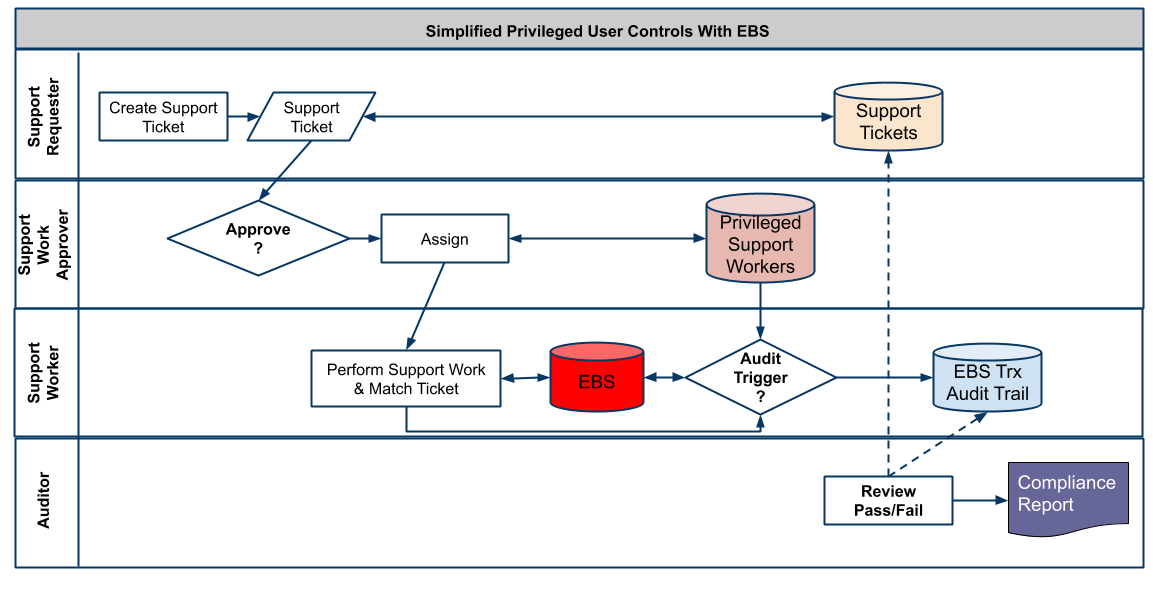
Independent financial auditors look for controls over what privileged users do in Oracle E-Business Suite (EBS) and to its database. Privileged users include business support, IT support and database administration staff. They have a high level of skill and are trusted to work on EBS, a critical asset. They have broader “powers” than EBS business users and are subject to fewer EBS application level and database controls. It is important to detect and know what they do, verify their actions are authorized by management and be able to mitigate improper activities, all in a timely manner. These privileged user controls are in the scope of Governance, Risk Management and Compliance (GRC).
Here are components of privileged user controls in the context of EBS and Oracle Database.
- Privileged Users.
- Authorization Processes for normal and emergency situations.
- Audit Trail of privileged user activities.
- Independent Review of these activities, for approval (Pass) or denial (Fail).
- Privileged User Control compliance reports.
Whether these controls are run by two or three people in a small organization or encompass several geographically distributed teams in a publicly traded global company, it is desirable and maybe necessary to graduate from spreadsheets, shared file repositories and emails to a shared and secure database application with workflow. It is logical to extend EBS and employ the Oracle Database.
Privileged Users
Who are they? DBAs, super users, business process owners, business and IT support staff. They have an EBS User account with numerous Responsibilities, including those for setups and configurations. They often perform Data Manipulation operations (DML) to change business or configuration data and Data Definition statements (DDL) to change the structure and operation of the database. Anyone with (a) “back end” access via SQL*Plus, SQL Developer, TOAD or Application Express (APEX) or “front end” access to certain Oracle Forms, like Oracle Alert, that allow SQL execution, is a privileged user.
Authorizations
Authorization is usually provided by “Ticketing” systems, where work is proposed, authorized and assigned to a privileged user. Since this may be time consuming, it is advisable to have an emergency “Break the Glass” process that can temporarily bypass the ticketing system. The privileged users are selected because of their skill and trustworthiness, and thus the access risk is acceptable in an emergency given the risk of the emergency itself.
Connect the ticketing system with the population of privileged EBS users and DBAs. The ticket explains why privileged users do something.
Audit Trail
Create an audit trail of both data and data dictionary changes. Record the basics: who did what when and where. Having looked at available functionality in EBS and the Oracle Database, we’ve found that database triggers are the optimal way to detect when a privileged user’s actions meet audit criteria, and to write the audit trail containing the basics.
Ensure the privileged users cannot tamper with the audit trails. This requires segregation of duties among DBAs.
Provide the privileged users the ability to connect their work session audit trails with the authorizing ticket.
Audit Review
Route the audit trail records to the approvers who review against support tickets. Workflow and timely emails are useful for this. In addition to pass/fail decisions, allow for a pending state when additional investigation is needed.
Compliance Reporting
Establish compliance reporting of ongoing authorization, audit trail and review activities as well as periodic (monthly, quarterly) summaries. The goal is to show that privileged user activities are being monitored and they are authorized by management.
Simplified Process: Actors, Activities and Data
About the Contributor
Absolute Technologies is an Independent Software Vendor providing applications that extend Oracle EBS in the GRC and Revenue Reporting areas. Founded in 1997. Committed to affordable, easily deployable solutions. Learn more at absolute-tech.com.

#EBS
#E-Business Suite
#Oracle Database